Attackers took over .edu subdomains at 34 major universities — and Google indexed the results under some of the most trusted domains on the internet.
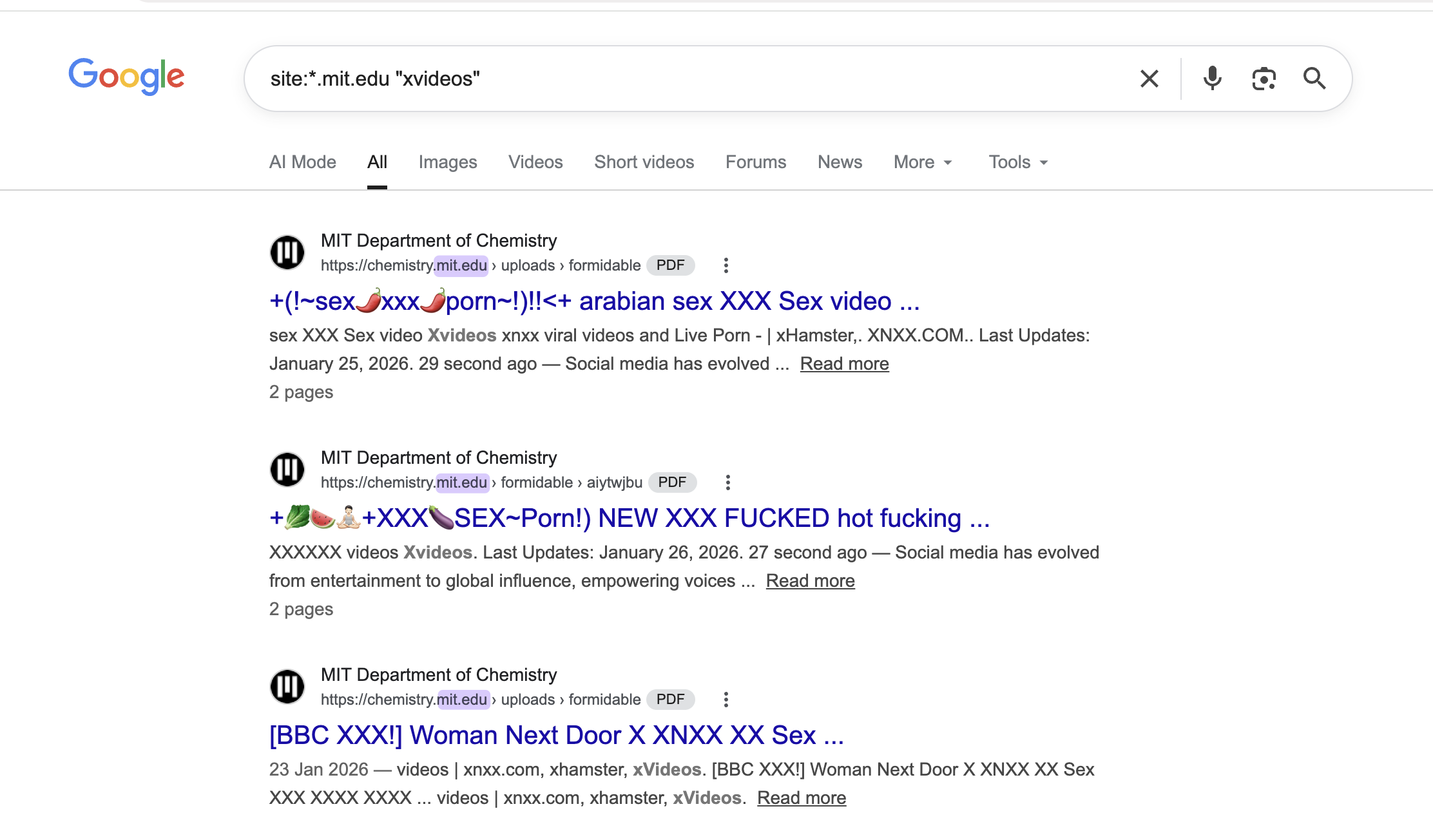
In early April 2026, I discovered a coordinated subdomain takeover campaign targeting major US universities. Attackers had hijacked subdomains at MIT, Harvard, Stanford, UC Berkeley, Columbia, UChicago, Johns Hopkins, and more than 25 other institutions — using them to serve explicit pornographic spam that Google was actively indexing under trusted .edu domains.
After I published my initial findings on LinkedIn, Infoblox VP of Threat Intelligence Renée Burton confirmed the campaign was the work of Hazy Hawk — a threat actor her team has been tracking since they hijacked CDC subdomains using the same technique.
A member of the security community also flagged that the Department of Defense Education Activity (DoDEA) — a DoD field activity operating under the Under Secretary of Defense for Personnel and Readiness — had a domain vulnerable to the same attack pattern.
The full list of affected institutions
Here are the 34 universities confirmed as impacted: MIT, Harvard, Stanford, UC Berkeley, Columbia, University of Chicago, Johns Hopkins University, George Washington University, University of Michigan, Rutgers, University of Virginia, Texas A&M, UC San Diego, Stony Brook University, Auburn University, University of Utah, University of Georgia, George Mason University, TCU, UCSF, Emory University, University of Washington, Washington University in St. Louis, Case Western Reserve University, UNC Chapel Hill, UNC Greensboro, Florida State University, Florida Southern College, Cal Poly, Antioch University, Ball State University, San Diego Supercomputer Center (SDSC), Atlantis University, and SIT.
That includes some of the highest-ranked universities in the country. And given the scale of the .edu domain space and the number of abandoned subdomains across thousands of US colleges and universities, this is almost certainly a fraction of the total.
How subdomain takeover attacks work
The technique is straightforward, which is part of what makes it so effective.
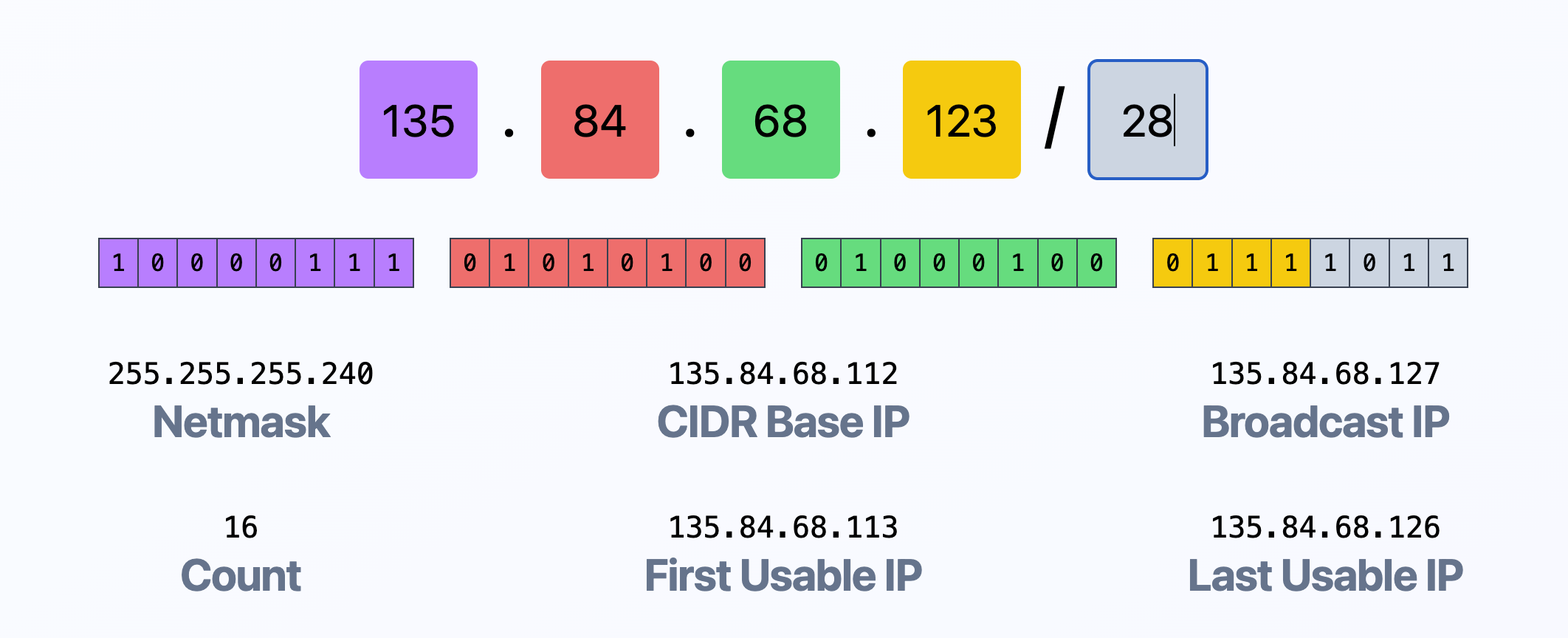
University IT teams create CNAME records that point subdomains to external services — GitHub Pages, WordPress via WP Engine, various cloud hosting platforms. A department sets up a project site, a research group launches a microsite, a student builds something for a class. Eventually the project ends, the person graduates or moves on, and the external hosting account gets deleted or abandoned.
But the DNS record stays.
The subdomain still points to the external service. The attacker scans for these orphaned CNAME records, registers a new account on the external platform that matches the abandoned target, and takes full control of what the university's subdomain serves.
For example, I found that www.ccct.uchicago.edu had a CNAME pointing to wp.wpenginepowered.com — a WP Engine hosted site that was no longer claimed. Anyone who registered the right WP Engine account could serve whatever they wanted under a University of Chicago subdomain.

What the attackers are doing with hijacked .edu domains
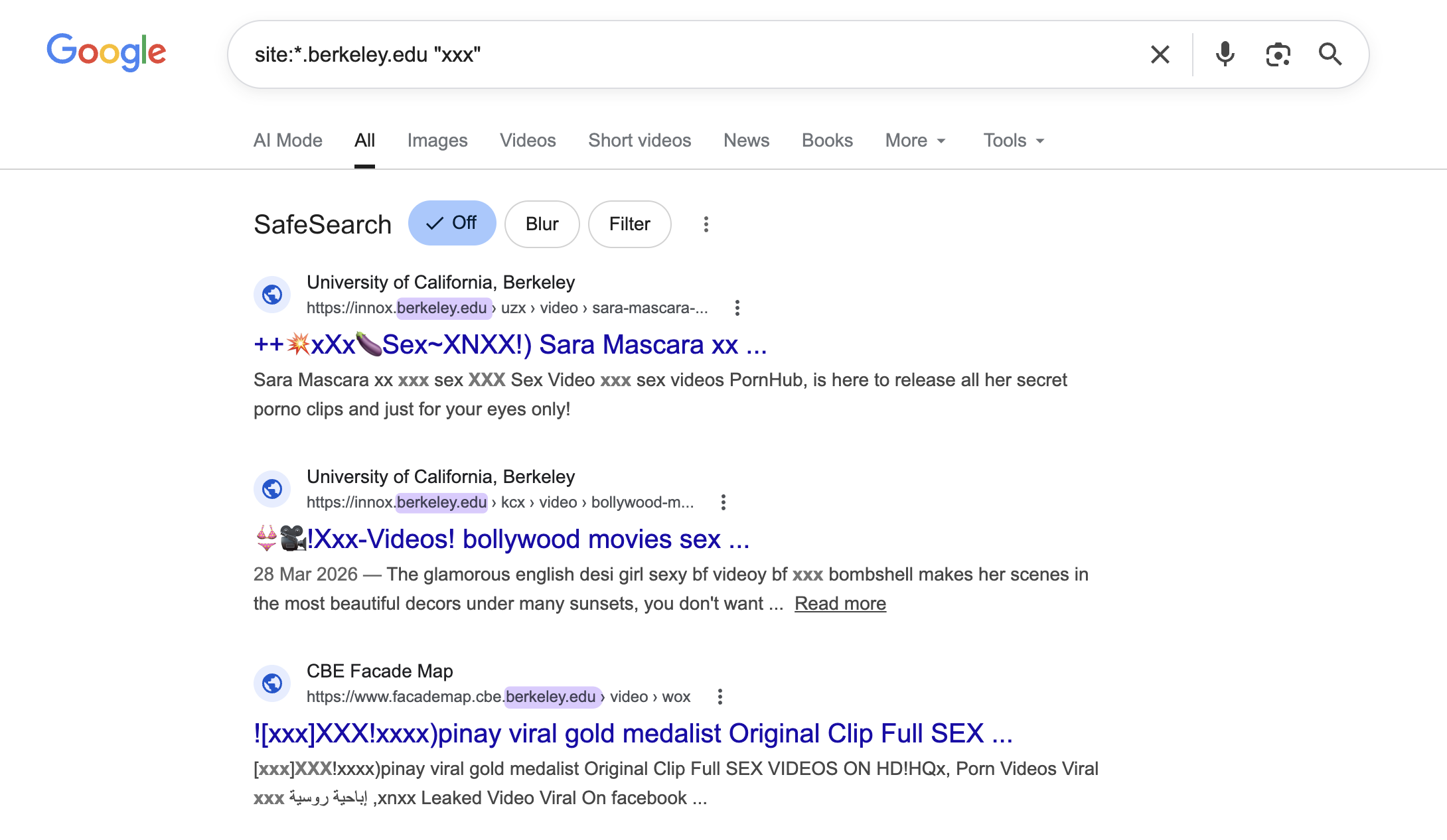
The hijacked subdomains are being used to host pages stuffed with explicit pornographic content and spam, optimized for search engines. Because .edu domains carry extremely high domain authority and trust signals in Google's ranking algorithms, these pages get indexed quickly and rank well.
The result: Google search results showing MIT Department of Chemistry, Harvard University, and UC Berkeley serving explicit adult content.
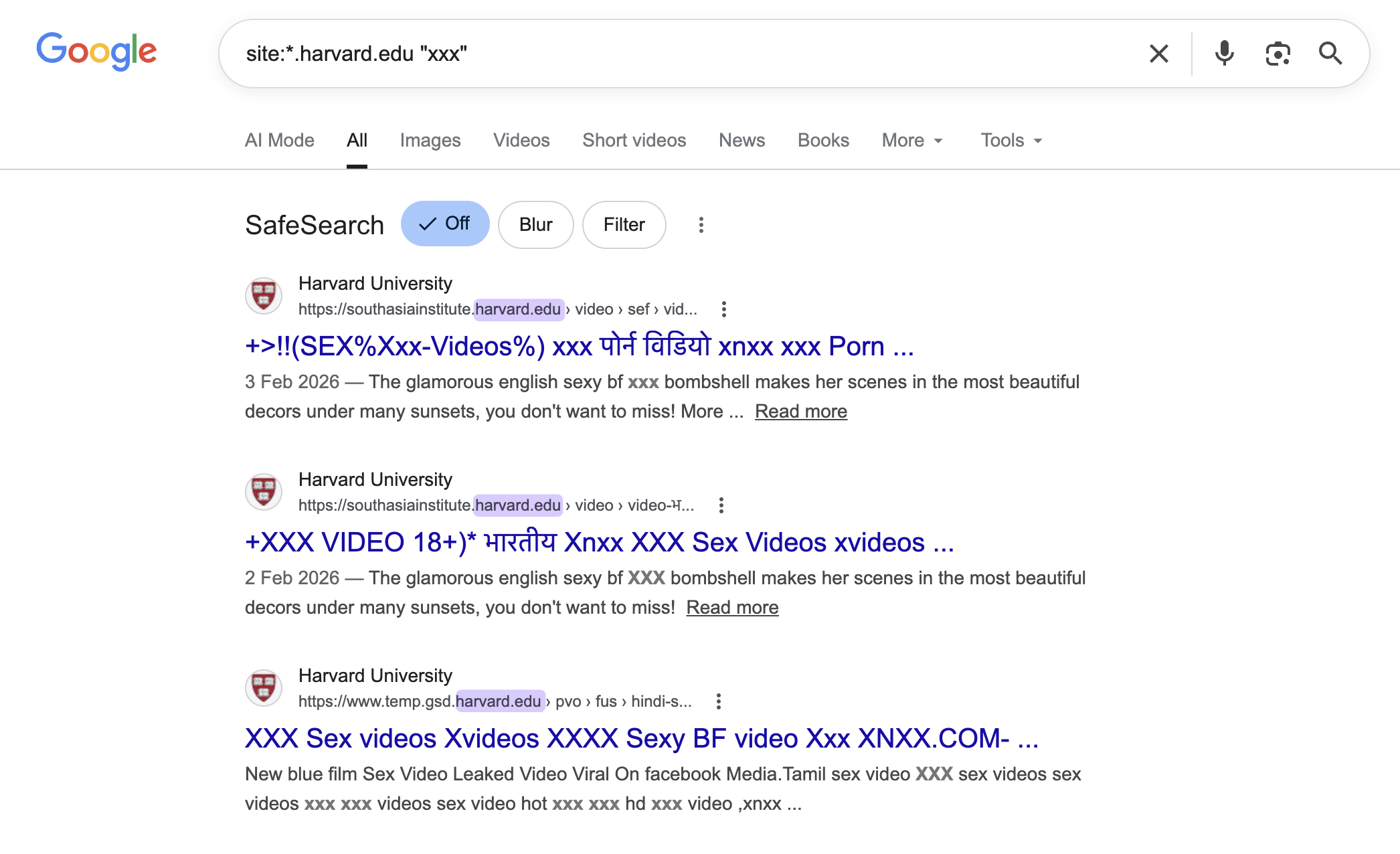
The pages drive traffic through sketchy affiliate advertising networks — the same monetization model Infoblox documented in their Hazy Hawk research.
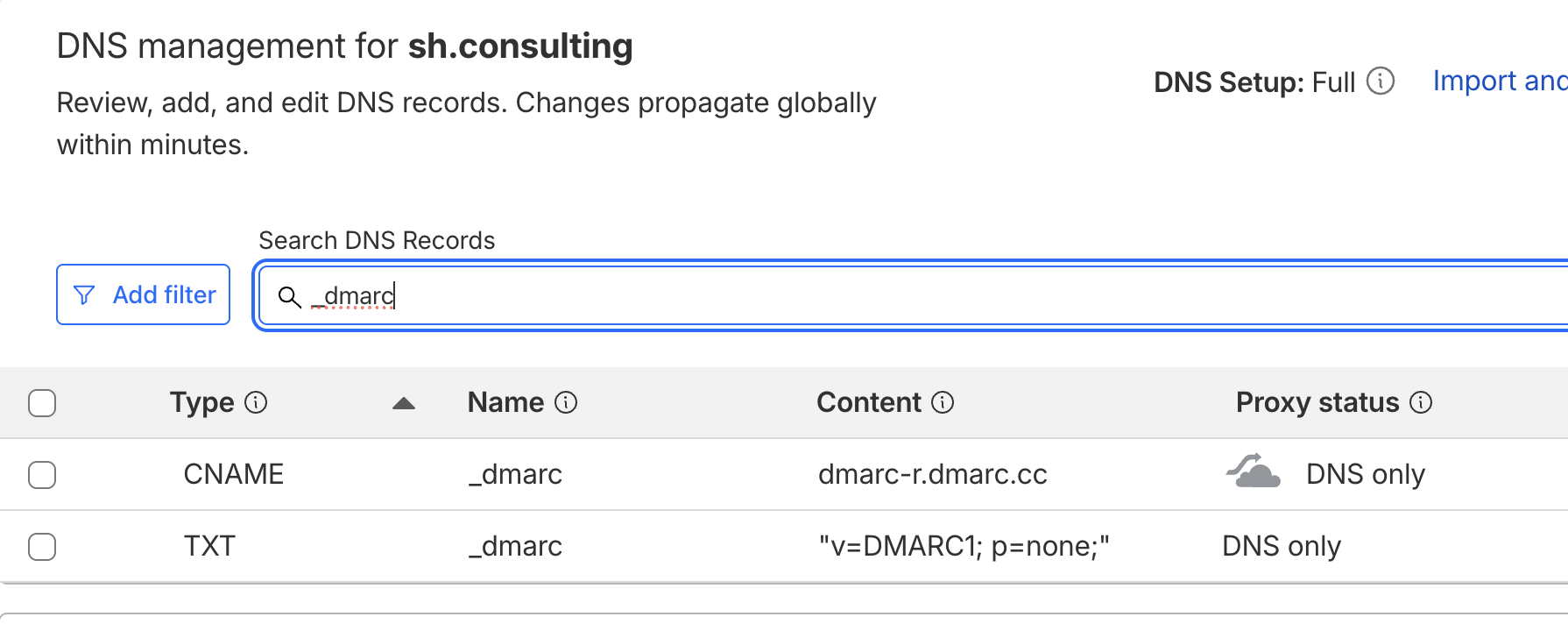
This is not just an SEO spam problem. Depending on the university's SPF, DKIM, and DMARC configuration, hijacked subdomains can also be exploited for email spoofing — potentially bypassing DMARC policies set to p=reject on the parent domain.
The Hazy Hawk connection
After I published my findings, Renée Burton — VP of Threat Intelligence at Infoblox — commented directly on my LinkedIn post, confirming the campaign matched the group her team has tracked as Hazy Hawk. She noted the actor systematically picks up dangling DNS records that can persist for years, exploits them, then drops them and repeats the cycle — driving traffic through sketch affiliate advertising networks.

Infoblox published extensive research on Hazy Hawk in 2025, documenting how the group systematically exploits dangling DNS records at government agencies (including the CDC), major corporations like Deloitte and PricewaterhouseCoopers, and now — as my research confirms — universities.
The DoDEA angle
After my LinkedIn post gained traction, security consultant Henk G. flagged in the comments that the Department of Defense Education Activity (DoDEA) — which operates schools for military families worldwide — had a domain vulnerable to the same pattern. This was reported through appropriate DoD channels.
The fact that the same vulnerability class extends from university research labs to military education infrastructure underscores how widespread the problem is.
Why dangling DNS records keep causing breaches
The root cause is simple: organizations create DNS records and never clean them up. There is no expiry date on a CNAME record. Nobody gets an alert when the target stops responding. And most university IT departments don't maintain a comprehensive inventory of their subdomains and where they point. We've documented this pattern beyond CNAMEs — Cloudflare's own DMARC documentation pointed administrators to an unregistered domain, and when we registered it and watched real reports start arriving from 22 production domains, the scope of the problem became clear.
This is compounded by how universities operate — they are highly decentralized. Individual departments, labs, research groups, and student organizations can often request subdomains independently. When people leave, there is no decommissioning process for the DNS records they created.
How to prevent subdomain takeover attacks
Every organization — not just universities — should maintain a documented DNS inventory covering all subdomains, CNAME targets, and the purpose of each record. Regular audits of CNAME records for dangling references are essential: any subdomain pointing to an external service that is no longer active should be removed immediately.
A decommissioning process that includes DNS cleanup should be triggered whenever projects end, staff leave, or external services are cancelled. Organizations should also monitor for unauthorized content appearing on their subdomains and review SPF, DKIM, and DMARC configurations to ensure subdomain takeovers cannot be leveraged for email spoofing.
Disclosure timeline
April 7, 2026 — Initial discovery and research published on LinkedIn
April 7, 2026 — Direct disclosure to George Washington University
April 8, 2026 — GWU remediated within 24 hours
April 8, 2026 — Renée Burton (Infoblox) confirms Hazy Hawk attribution
April 8, 2026 — DoDEA vulnerability flagged by community member, routed to DoD contacts
This research was conducted by Alex Shakhov, founder of SH Consulting, a DNS security and email deliverability consultancy. The discovery was a byproduct of routine security research work for clients across the US and Canada. For questions, reach out at hello@sh.consulting or book a call.