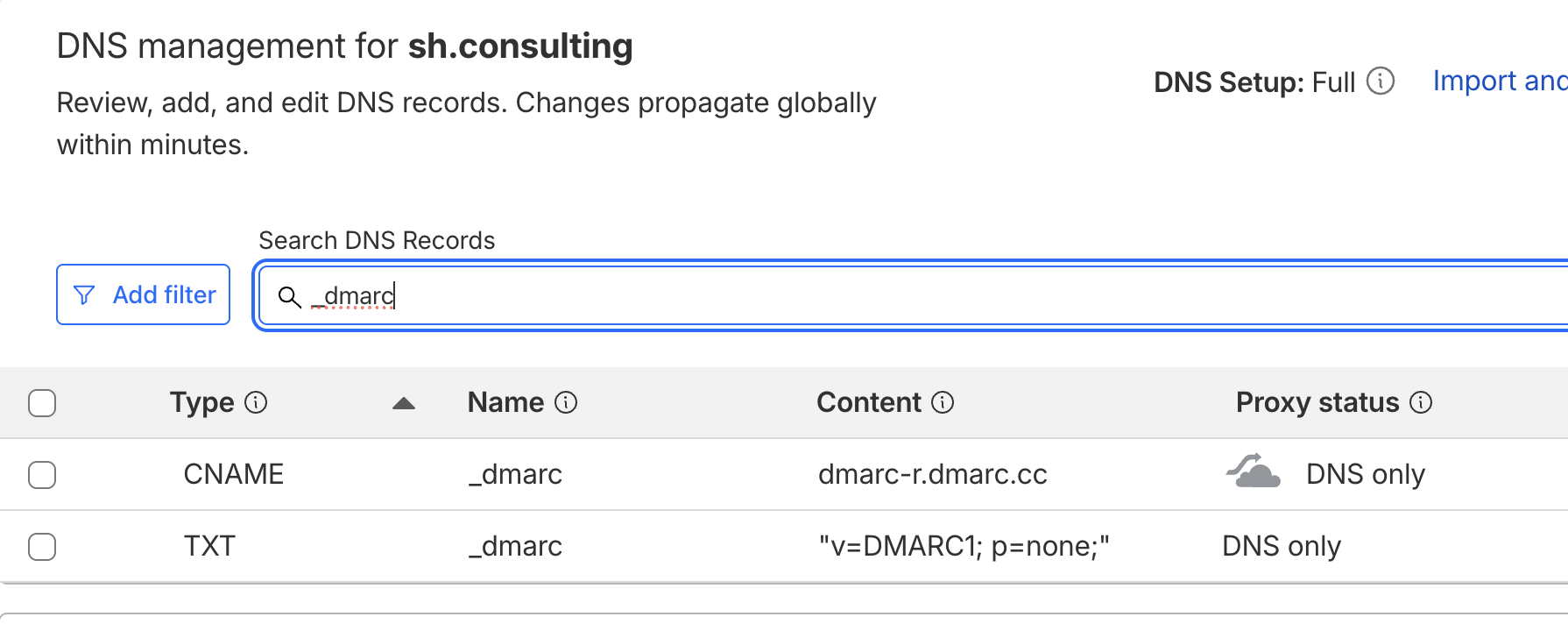
Cloudflare included a publicly available domain in their technical documentation, which has led dozens of organizations to implement the suggested DNS record in their DNS zones without understanding the risks.
Rather than using an IANA-reserved example[.]com to illustrate DMARC deployment logic, the documentation references third-party-example[.]com.
This domain has never been registered (until we did), meaning any party could acquire it and gain access to infrastructure data from organizations that relied on the documentation.
I see two primary concerns:
1. The documentation does not clearly indicate that the domain must be replaced prior to production deployment.
2. The example domain is neither controlled by Cloudflare nor reserved by IANA, creating an unnecessary security exposure.
I initially considered reporting this to Cloudflare, but their vulnerability disclosure program on HackerOne explicitly classifies this type of issue as out of scope.
As long as organizations treat DMARC as a copy/paste configuration rather than a security control, exposures, data leakage, and abuse opportunities for threat actors will remain inevitable.