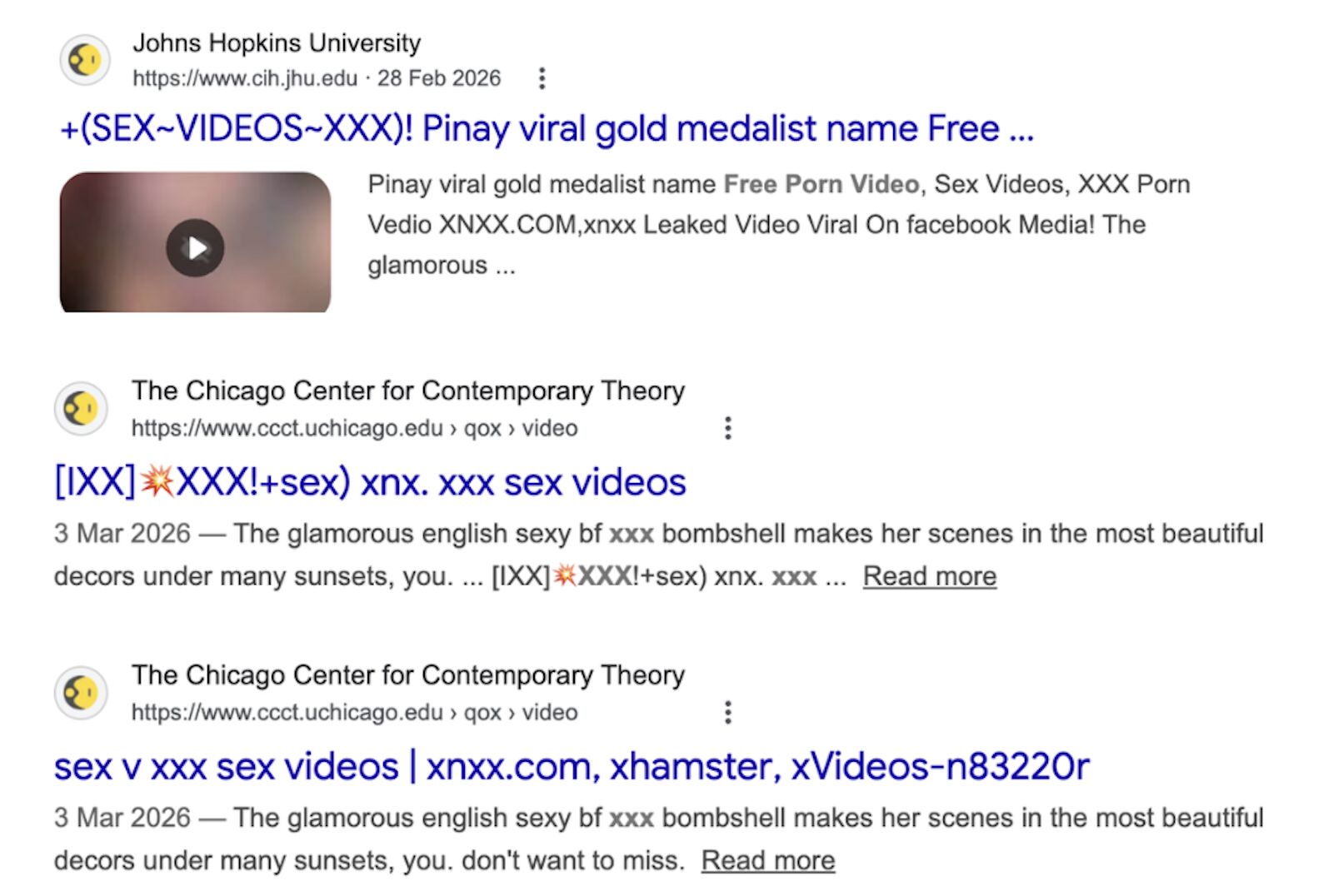
There's a coordinated subdomain takeover campaign targeting US universities - Johns Hopkins, UChicago, Florida State, and 10+ others.
Attackers are hijacking .edu subdomains and serving explicit spam that Google is indexing under trusted university domains.
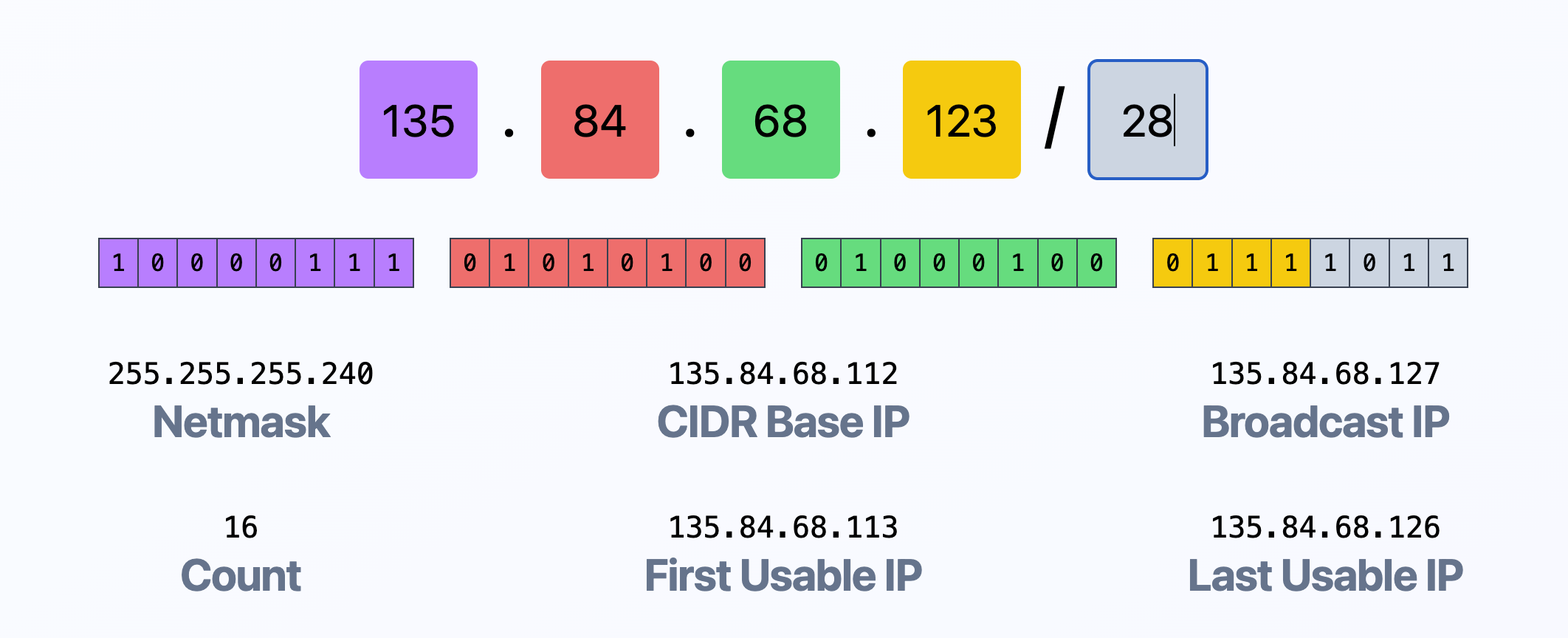
University IT teams create CNAME records that point subdomains to external services (GitHub, WP, etc) . A student sets up a project site, graduates, and the site gets abandoned. But the DNS record stays.
They scan for orphaned CNAMEs, register the abandoned accounts on the external platform, and take full control of the university's subdomain.
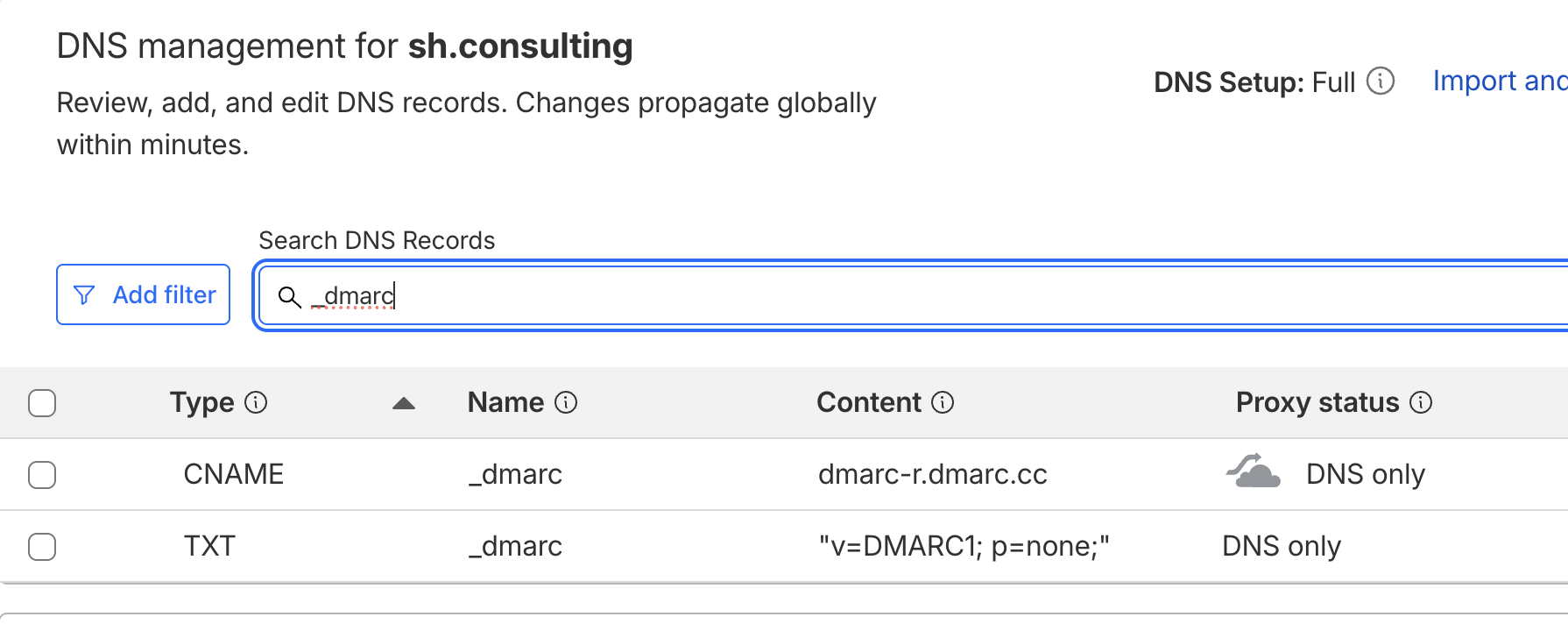
As a result, malicious pages are ranking in Google under .edu domains & attackers get the SEO authority of a .edu for free + depending on the SPF, DKIM, and DMARC, hijacked subdomains can be exploited for email spoofing, bypassing p=reject for DMARC.
It's a good call for every organization to maintain a documented DNS map - subdomains, CNAME targets, forwarding rules, and redirect logic, and enforce a standardized process for creating, reviewing, and decommissioning DNS records.