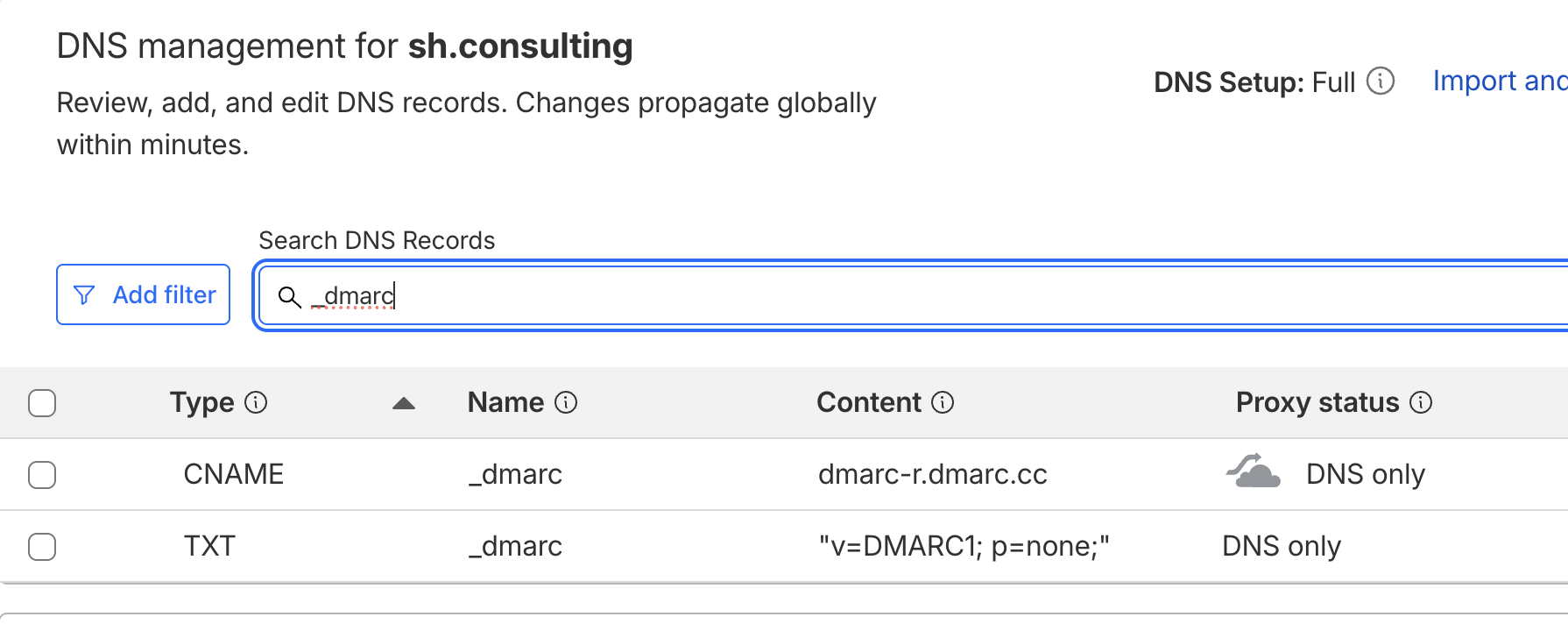
Threat actors leveraged the Riddle Technologies AG platform to obfuscate malicious URLs in email and bypass spam filters. The email template mimicked an encrypted Mimecast message: shconsult.ing/njZs4vtm
All embedded links redirected to an intermediary landing page hosted on Riddle and from there, pointing to a phishing page hosted at the .sa[.]com TLD, managed by CentralNic Registry: shconsult.ing/81QRbk2w
Victims clicking "sign documents" were routed through CAPTCHA before reaching a credential harvesting page impersonating Gmail login: shconsult.ing/f48zvJb5
The campaign employed redirect chains, abusing legitimate infrastructure to obscure malicious endpoints.
Forensic analysis indicates the spoofed domain has been active for at least 26 days: shconsult.ing/45x9g0c3