This is how security actually works in client organizations (kidding, there’s no security):
A SaaS platform hosts white-labeled pages for client organizations, where end users browse products and set up notifications.
When a new item is added to the platform, the system fires off an email notification.
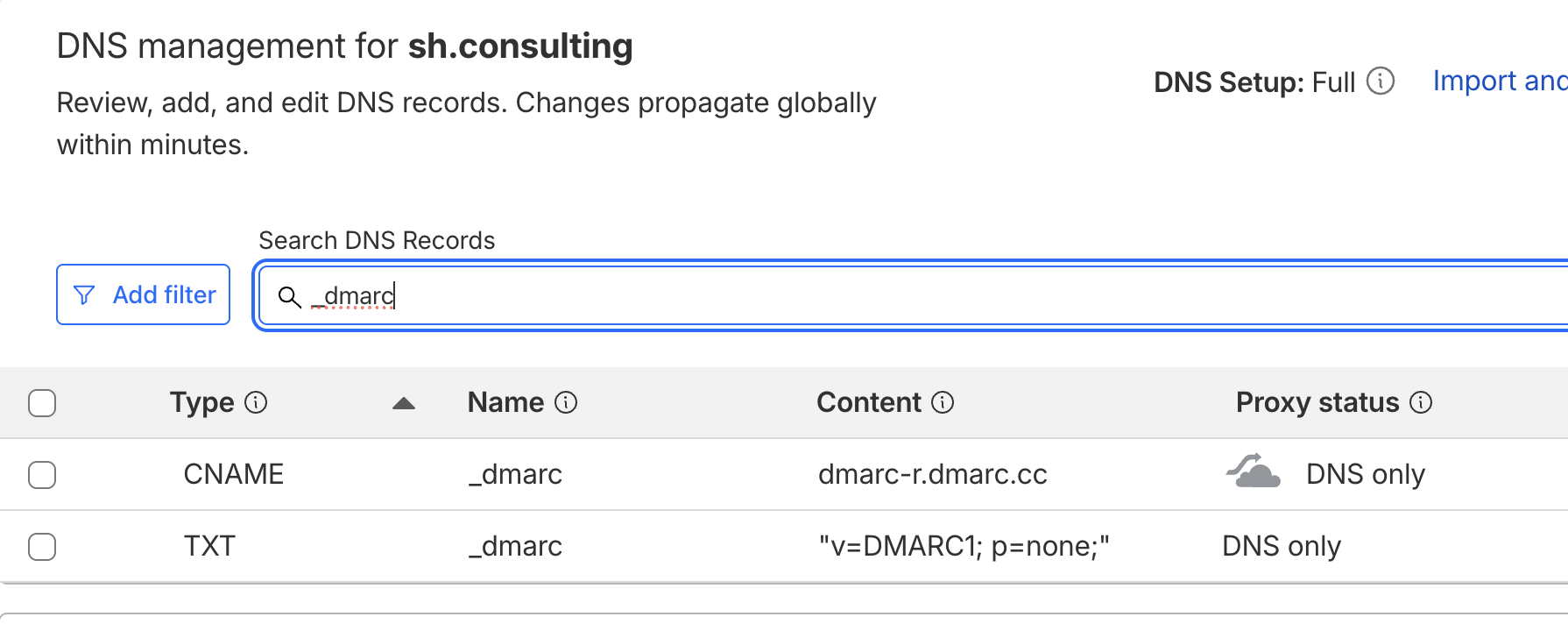
But the email doesn't come from the client's domain - it comes from the SaaS platform's domain, with only the "friendly from" name showing the client organization's brand.
This creates a vulnerability that bad actors are actively exploiting.
An attacker finds any publicly searchable customer-facing page through Google. They register as an end user and enable every available notification type. Then they:
- Enable every notification type (instant, daily, biweekly, weekly, etc)
- Add random email recipients
- Customize subject lines to impersonate PayPal / invoices, Stripe / password resets, etc
- Embed phishing links, etc
An instant spam bomb is distributed through legitimate Sendgrid infrastructure. Every malicious email passes through because it's coming from a "trusted" SaaS domain.
Doesn’t seem like a regular config bug but rather an architectural flaw. A series of poor design and engineering decisions that put both the platform and their clients’ reputations at risk.
I don’t see an easy fix, but the first thing I’d do is restrict customization of notification alerts.