How a single DMARC misconfiguration can be exploited to launch an email-based DDoS attack.
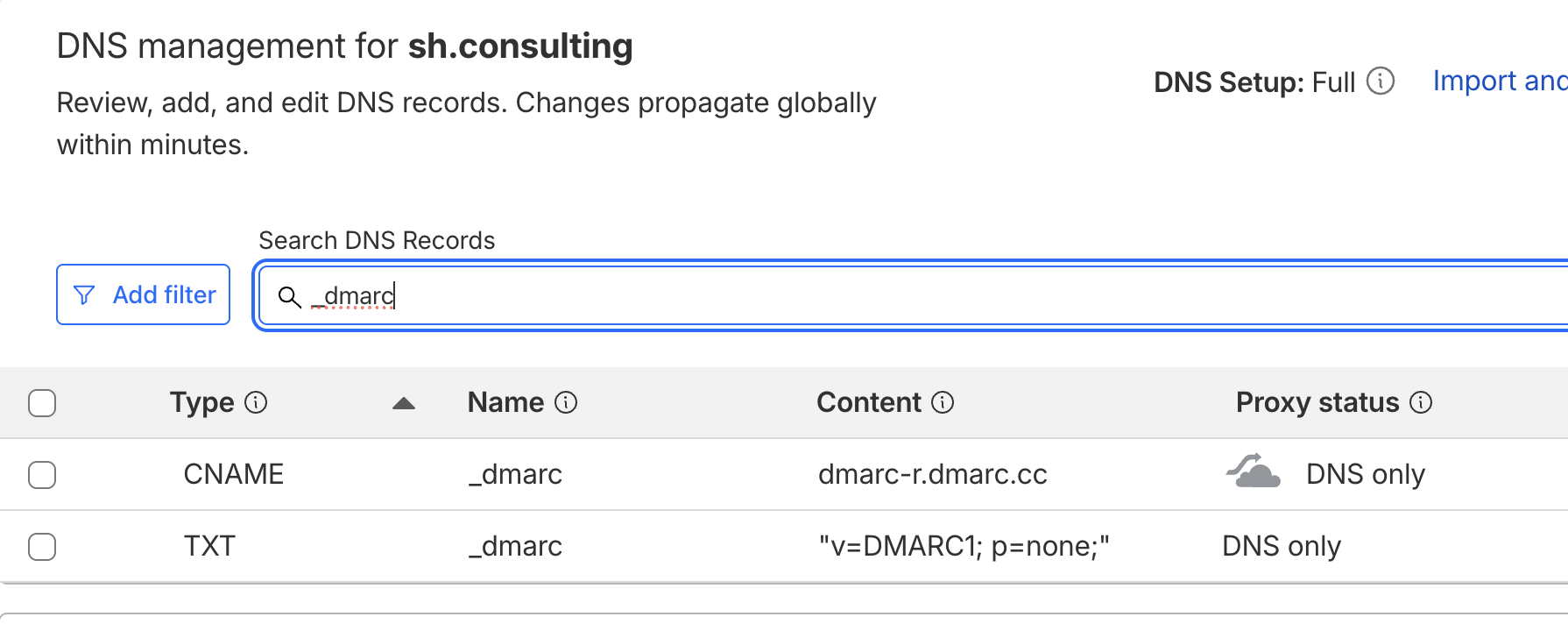
Many companies want to receive DMARC reports for all their subsidiaries in one centralized email account. They often use a wildcard EDV record instead of defining an explicit hostname, which creates a high-risk entry point.
Exploit:
- today, 5,000+ mail servers send DMARC aggregate reports
- if an attacker registers a throwaway domain and sets its DMARC RUA to a wildcard EDV-enabled domain, reports are redirected to your internal mailbox
- one email sent per server = 5,000 reports the next day
- 10 throwaway domains = 50,000 inbound emails per day
- they loop it
- all reports come from trusted companies with authenticated domains: Google, Microsoft, Yahoo, etc.
This is real email-based DDoS aka spam bombing. It causes:
- server slowdowns
- missed legitimate emails
- team inboxes flooded with junk
- engineering resources wasted on mitigation and cleanup
- organizations running out of cloud storage
Fix:
- never use a wildcard EDV record for your main domain
- always define specific hostnames that you control
- ensure your infrastructure can’t be co-opted into someone else’s feedback loop
.DMARC is a good and incredibly helpful standard but there are still many ways it can be turned against companies.
Watch your DMARC.