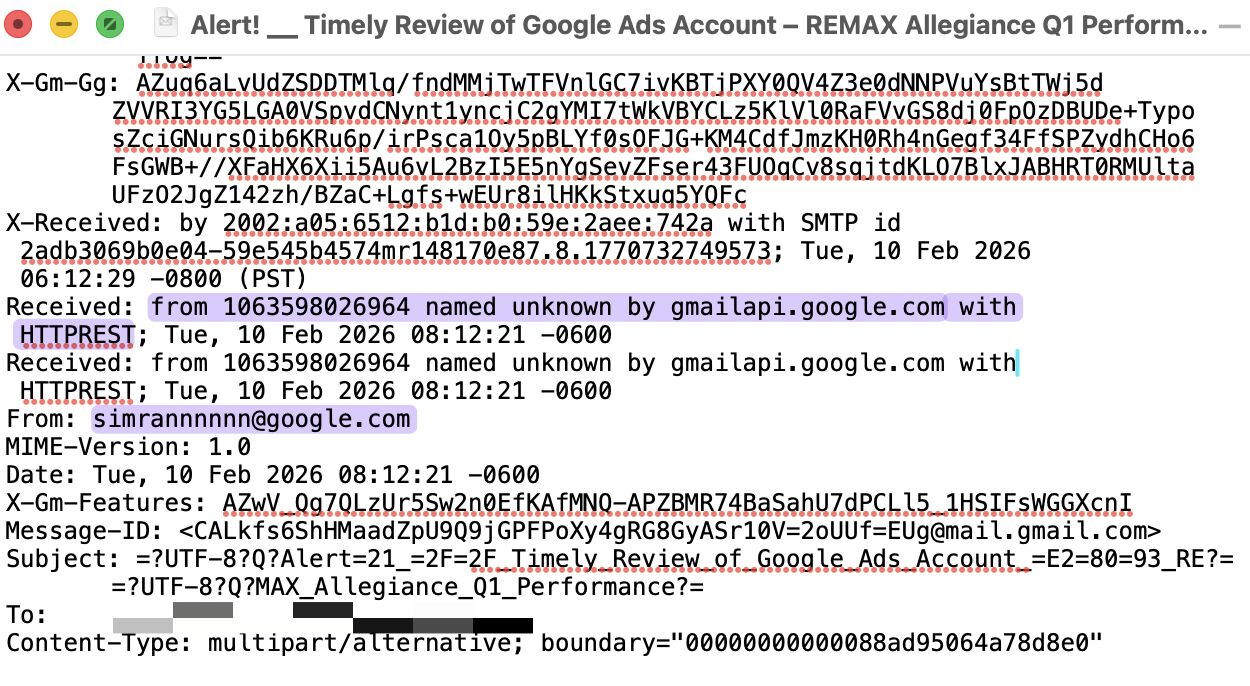
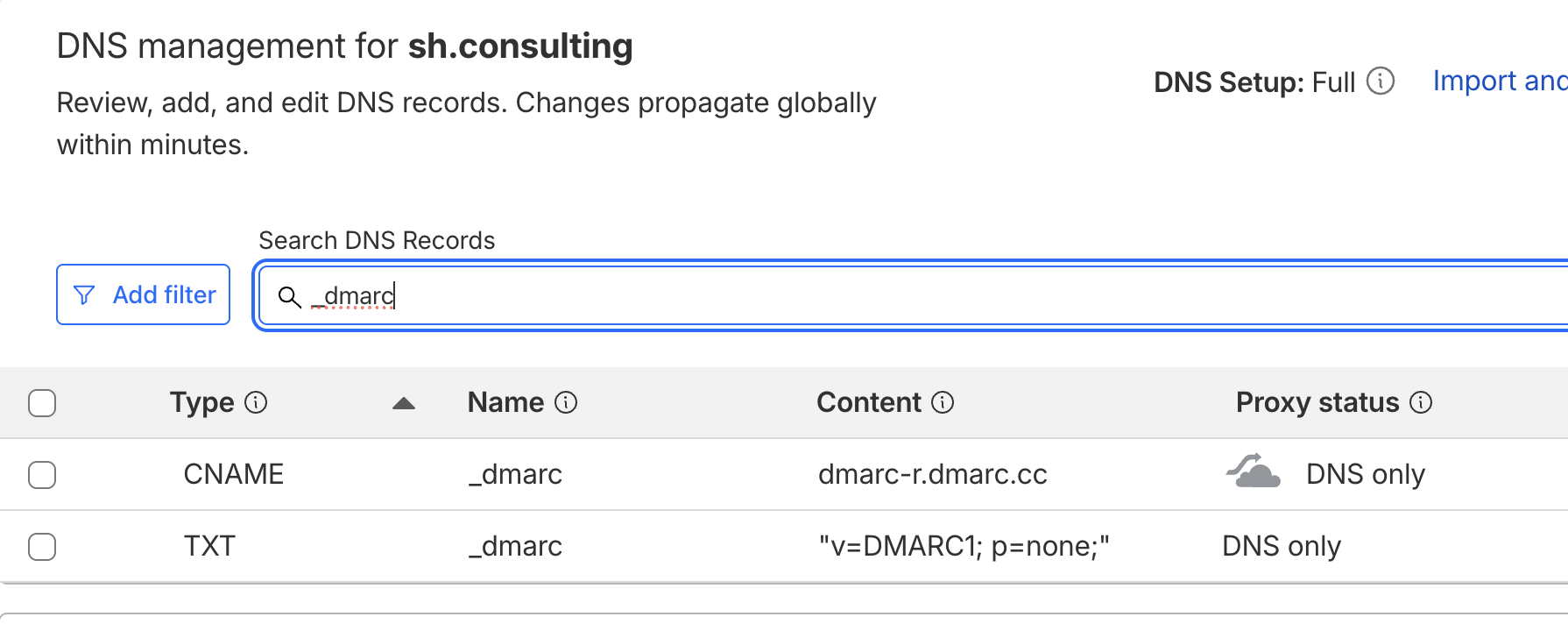
Someone just sent a scam email from @google[.]com through the Gmail API with DMARC p=reject passed, DKIM signed by Google, and SPF authenticated, bypassing several internal security controls.
Urgency in the subject line, a request to review Q1 ads performance, tailored to the victim's industry, expecting them to reply. No phishing links, payloads, or attachments were inside.
For this scam to work, the threat actor must have access to a @google[.]com mailbox and be able to read incoming replies and continue the conversation.
But this wasn't a classic BEC. No Google account was taken over.
Attacks are getting more sophisticated.