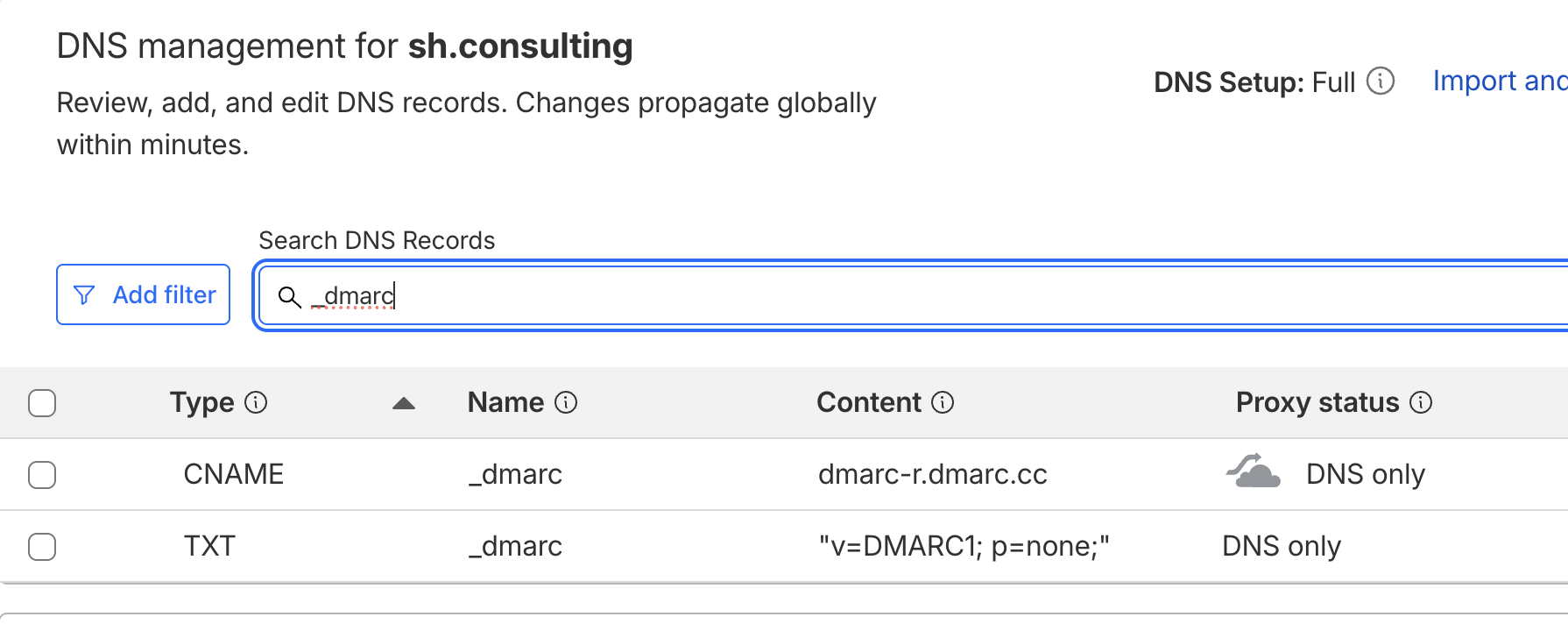
A UK-based payment platform, integrated with over 16,000 banks and backed by Mastercard and Barclays, has been sending DMARC reports to an exposed email endpoint.
After several months of unsuccessful reporting, we registered accessspay[.]com to prevent potential data exposure. The issue is not just AccessPay not monitoring their DMARC reports for spoofing & phishing incidents, but that reports were directed to a domain that could’ve been registered by a threat actor to map infrastructure, access communication patterns, recipient data, and traffic volumes.
We never enabled mailboxes for accessspay[.]com, but it’s highly likely an accept-all inbox could have received a large volume of customer communications.
The last DMARC update appears to have been in early 2024, suggesting there isn’t even an annual DNS audit in place that would reveal further issues.
No matter the size of your organization, whitelisting exposed servers in DNS is not a good practice and can definitely have consequences.
Update: a few hours ago, AccessPay silently updated their DMARC policy, removing the exposed reporting endpoint from the RUA tag, leaving the organization blind to email security incidents.